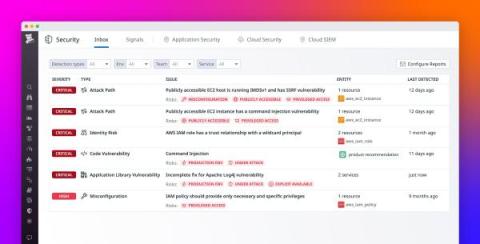
How Datadog Security Inbox prioritizes security risks
In November 2023, Datadog announced the launch of Security Inbox, a solution that equips security and engineering teams with valuable insights for mitigating security risks. Security Inbox takes the guesswork out of addressing the most pressing security risks by automatically organizing them into an actionable list for remediation. As of today, Security Inbox has already served thousands of security and engineering teams, giving them the right context at the right time for protecting their environments.