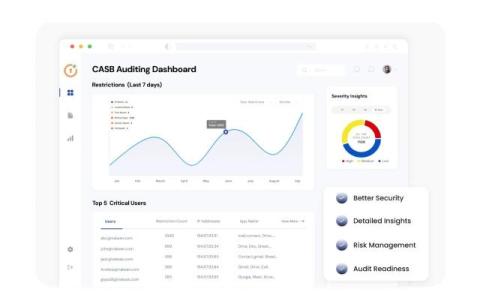
CASB Auditing: A Must-Needed Feature for Cloud Security
Let’s understand the CASB Auditing feature and how organizations can monitor and log every user action—from file access to policy violations—giving them a clear and actionable trail for analysis.