Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest News
Vuln of the Month: CVE-2020-10148 SolarWinds Orion Authentication Bypass
Every week, our global community of hand-picked Detectify Crowdsource ethical hackers submit new vulnerabilities that we make available to our users as automated security tests. In the new series Vuln of the Month, we deep-dive into an especially interesting vulnerability that was added to our scanner in the past month. First up: CVE-2020-10148, SolarWinds Orion Authentication Bypass. In January, Detectify added a security test for CVE-2020-10148, SolarWinds Orion Authentication Bypass.
The Root of Your AWS Insecurities
The AWS root account can do anything in your account, and it follows that it should be protected with tight security controls: However, while analyzing root account configuration and use in 915 accounts from 153 production environments over four months, we found that: We will now look at the data in more detail to understand more of the nuances and learnings, including the tradeoffs and the presumed “why’s” behind the problems.
Preventing CSRF Attacks
Cross-site request forgery (CSRF, sometimes pronounced “sea surf” and not to be confused with cross-site scripting) is a simple yet invasive malicious exploit of a website. It involves a cyberattacker adding a button or link to a suspicious website that makes a request to another site you’re authenticated on.
Industry-First Pay-as-you-go SaaS Platform for Kubernetes Security and Observability
We are excited to introduce Calico Cloud, a pay-as-you-go SaaS platform for Kubernetes security and observability. With Calico Cloud, users only pay for services consumed and are billed monthly, getting immediate value without upfront investment.
Evaluating MySQL Recursive CTE at Scale
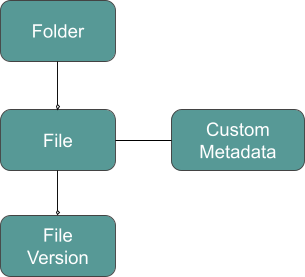
Egnyte is a unified platform to securely govern content everywhere. We manage billions of files and petabytes of content. One of the core infrastructure components powering such a scale is called MDB or metadata database. It is a cluster of hundreds of MySQL instances storing billions of metadata records. It stores information about files, versions, folders, custom metadata, and their relationships.
Don't let AppSec tool overload slow down your development
Application security testing tools help developers understand security concerns, but having too many tools can do more harm than good. Good tools are essential for building just about anything. But maybe that needs a bit more clarification: Not just good tools. They also have to be the right tools. Because the old cliché, “if all you have is a hammer, everything looks like a nail,” is a warning that using the wrong tool can mess everything up.
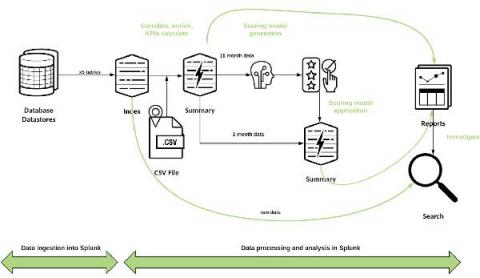
Creating a Fraud Risk Scoring Model Leveraging Data Pipelines and Machine Learning with Splunk
According to the Association of Certified Fraud Examiners, the money lost by businesses to fraudsters amounts to over $3.5 trillion each year. The ACFE's 2016 Report to the Nations on Occupational Fraud and Abuse states that proactive data monitoring and analysis is among the most effective anti-fraud controls.
The what, why, and how of using network IP scanners in IP-centric IT infrastructures
A simple command-line interface (CLI) ping will give you details about your target IP address. However, you may have to input the ipconfig command, and then the arp-a command to fully discover the status of an IP, and this is just for one IP address. Now imagine doing this for an IP block of 300 IPs, or even 50 IPs, or doing the same task periodically to manage your IP pool of thousands of addresses and their metrics. Seems like an Herculean task for any network admin!
CISOs report that ransomware is now the biggest cybersecurity concern in 2021
As the number of remote working arrangements rose substantially in the last year, cybercriminals were quick to take advantage of these new opportunities. Spam and phishing emails increased in number even more rapidly than telecommuting, and company cybersecurity officers found themselves struggling to keep up. Phishing emails often came with a sinister sidekick - a ransomware attack.