Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest News
Announcing automated fixes for vulnerabilities in .NET dependencies
We’re pleased to announce improved support for.NET applications in Snyk Open Source, allowing developers to fix vulnerabilities in.NET dependencies with the help of actionable advice and automated pull requests! As of the time of writing, NuGet, the Microsoft-supported and de-facto standard package manager for.NET, has 276,266 unique packages, downloaded on average more than a billion times a week!
What is DevOps and DevSecOps?
Among its evangelists and advocates, DevOps is about the cultural shift from traditional silo groups to the integration of a DevOps team. DevOps teams speak about change, feedback, inclusiveness, and collaboration. The goal is to bring everyone who has a seat at the table onto a common platform to work together and deliver changes to business systems safely and securely. Companies that choose to go through digital transformation use DevOps as their platform to deliver software at speed and scale.
How to prevent Trojan Source attacks with Snyk Code
Earlier this month, a group of researchers at the University of Cambridge published an academic paper, with an accompanying website, on a new type of potential vulnerability that could appear in source code. They called it Trojan Source.
SecurityScorecard Supports the Proposed Interagency Guidance on Third-Party Management for Banking Organizations
On July 19, 2021, The Board of Governors for the Federal Reserve System (Board), the Federal Deposit Insurance Corporation (FDIC), and the Office of the Comptroller of the Currency (OCC) released their proposed interagency guidance around third-party risk management. SecurityScorecard submitted comments in response to the proposal urging the agencies to include the adoption of security ratings to mitigate the cyber risk to financial institutions introduced by third-party vendors and suppliers.
Supply Chain Cybersecurity: Risk Management Best Practices
Supply chain logistics have been the backbone of global trade for hundreds of years. Extending the same concept, with the added digital components gives birth to supply chain cyber security risks. Supply chain cyber security is a topic that has come into the limelight for the last couple of years.
What is Configuration Management? Importance and Tools
Configuration management (CM) is a process that helps maintain the consistency of software versions and configurations across various environments. It is usually associated with the concept of change control. Configuration management systems help ensure that changes to an application are correctly documented, authorised, tested and deployed in a controlled manner to avoid errors.
The Microsoft Power Apps Portal Data Leak Revisited: Are You Safe Now?
In late August 2021, a major data leak exposed where 38 million private records through Microsoft’s Power Apps portals, a powerful low-code tool that enables both professional and citizen developers to create external-facing applications. The misconfiguration was discovered by the research team at UpGuard and is now well-known as one of the most severe low-code security incidents to date.
The Importance of Speed During Detection and Response: Iranian-Backed Hackers Targeting U.S. Companies with Ransomware
Iranian government-sponsored advanced persistent threat (APT) actors are exploiting known Microsoft and Fortinet vulnerabilities to attack targets with ransomware in the transportation, healthcare and public health sectors, according to an alert issued on Nov. 17 by the Cybersecurity and Infrastructure Security Agency (CISA).
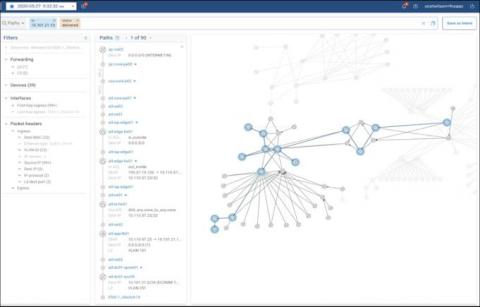
Make the Headlines for Good News - Not a Security Mishap Due to Config Drift
The risk of config drift is ever present. And when you consider that modern enterprises have incredibly complex and ever-changing networks with thousands of devices, from routers to firewalls to switches, running billions of lines of config, it’s easy to understand why. Networks are constantly being changed by people - who though well intentioned - make mistakes. A configuration change that accomplishes the immediate goal may take the network out of compliance, but how would anyone know?