What is SIEM? A guide to cyber Security Information and Event Management
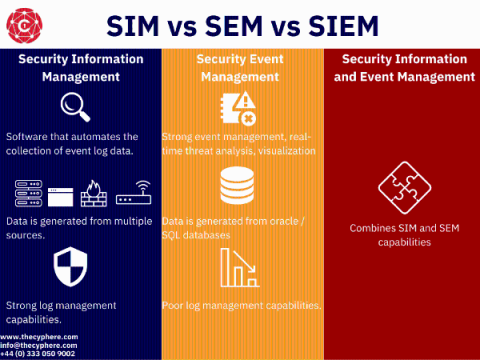
Security information and event management refer to Security Information Management (SIM) and Security Event Management (SEM) through a single pane of glass. SIEM solutions are used by security analysts to monitor any potential threats within the infrastructure of their organisation.