Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest News
Two Critical Vulnerabilities Impacting GitLab Community Edition and Enterprise Edition
GitLab has addressed two critical vulnerabilities in the GitLab Community Edition and Enterprise Edition that require immediate attention.
Key Cybersecurity Insider Threat Indicators to Pay Attention To
The 2023 Global Cybercrime Report: A look at the key takeaways
Tips for Ensuring HIPAA Compliance
Cyber Security Advice For The Property Sector
Leveraging her extensive experience in the cyber industry and a talent for creative writing, our Marketing Assistant adeptly translates complex, technical cybersecurity concepts into compelling, informative content that not only engages you, the reader, but also underscores our authoritative position and expertise in the industry.
Good Application Security Posture Management Requires Great Data
Discover how GitGuardian enhances Application Security Posture Management, ASPM, with top-notch code security and secrets detection and remediation coordination.
Androxgh0st Malware: SafeBreach Coverage for US-CERT Alert (AA24-016A)
On January 16th, the Federal Bureau of Investigation (FBI) and the Cybersecurity and Infrastructure Security Agency (CISA) issued an urgent advisory to highlight the ongoing malicious activities by threat actors deploying the Androxgh0st Malware. Detailed information about these activities and the associated indicators of compromise (IOCs) and the various tactics, techniques, and procedures (TTPs) is listed in Known Indicators of Compromise Associated with Androxgh0st Malware.
Datadog's approach to DevSecOps: An executive perspective
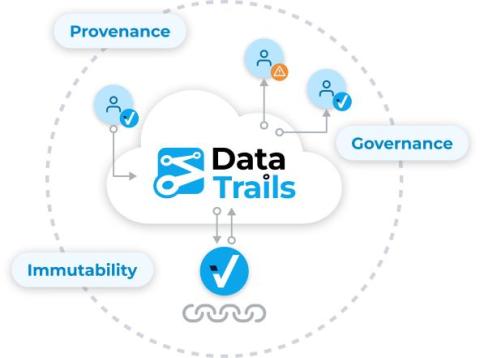
DataTrails: Sharing and Verifying Immutable Audit Trails
To share an immutable audit trail, you can do this with a link or a QR code that is automatically created when provenance and authenticity metadata is recorded in your DataTrails account. After you sign in to your DataTrails account on your smartphone, Anyone can use Instaproof or the DataTrails API to verify the authenticity, provenance and audit trails of public images.