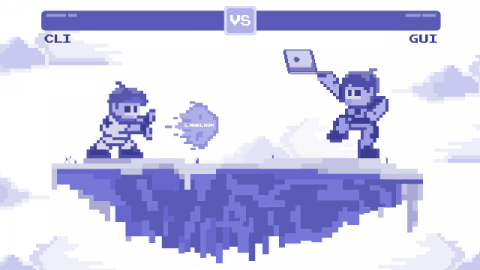
How I Found Myself in a Command Line vs. GUI Meeting
“Ev, do you have time later today to discuss the new web GUI for the command line terminal?” said the Slack message. It came from Alex, our user experience chief and the product in question is the SSH client. Part of me was worried. The command line environment had a sanctuary where I found peace and happiness away from the world of browser-based tools.