Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
AST
Why do we need a new approach to SAST?
Many companies provide legacy static application security testing (SAST) tools or engines, but their usefulness has not kept pace with the needs of an application-driven world. In order to succeed, businesses need a modern approach to SAST that will greatly improve it’s value in the software development lifecycle. In this blog, I look at the problems with traditional SAST tools, why there needs to be a change of approach in the SAST market, and what the future holds for SAST.
7 Challenges of Embedded Software Security Testing in 2023
We live in a world that depends on embedded software. It’s in the cars we drive, the elevators we take and the airplanes we travel in. As these systems become more and more complex, it becomes increasingly challenging to ensure that the interaction between embedded software and hardware remains functional and secure. Due to the nature of embedded systems and the devastating consequences of failures, many traditional testing methods fall short of providing adequate security for them.
How Code Coverage Helped Me Find 3 SQL Injections
An 8-Step Application Security Risk Assessment Checklist for 2023
As organizations are increasingly prioritizing application security continues to become a top priority for organizations, application security risk assessments is atop many bucket lists. Every application is unique and carries threats factors. It's critical to implement processes and tools to identify and remediate security issues before shipping.
My New Year's Resolution As A Java Dev | Code Intelligence
Effective Unit Testing for Java Applications: Common Challenges and Solutions | Code Intelligence
How to Find Bugs In Java at Scale With CI Fuzz CLI and JUnit | Code Intelligence
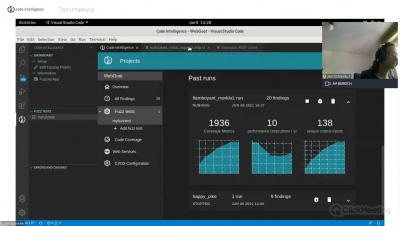
How to Maximize the Value from Your SAST Tool
It stands to reason that if you’ve implemented a Static Application Security Testing (SAST) tool, you’ll want to reap the full value of the investment. But to accurately assess ROI, you need metrics that can evaluate factors such as overall results, KPI compliance, and timeframe. Only then can you estimate whether you’re making a real improvement to the security of your code base, and from that, assess the monetary value of these results.