Is IAM, SIEM, and DLP Enough to Combat Insider Risk?
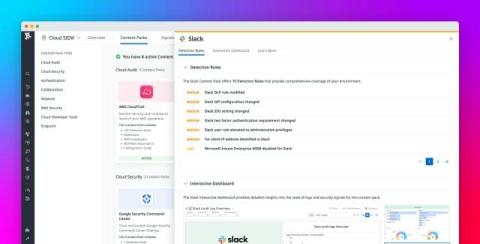
Despite significant investments in cybersecurity tools like Identity and Access Management (IAM), Security Information and Event Management (SIEM), and Data Loss Prevention (DLP), insider risks continue to grow. Why? These tools primarily focus on actions, logs, and event recognition rather than taking a deep, sophisticated approach to understanding human behavior over time. Insider threats—whether from negligence, malicious intent, or compromised users—are notoriously difficult to detect.