Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
January 2023
Application Security Requires Concerted, Continuous Efforts
According to Forrester Research, applications are the top cause of external breaches because cybercriminals consider them to be one of the easiest entry points to attack organizations’ code bases. As supply chain attacks increase, it has become increasingly important for organizations to implement and maintain a continuous application security program and make it a priority.
The State of Application Security Q4 2022
App Security & Compliance for SaaS Companies in Saudi Arabian Market
Datadog on the Lifecycle of Threats and Vulnerabilities
WhiteHat Dynamic Application Security Testing (DAST) | Synopsys
This Month in Datadog: Cloud Security Controls Ruleset, New Test Coverage Page, and more
Application Security Technology Predictions 2023 with Chris Wysopal
AppSec Playbook for 2023
Building a Modern Application Security Strategy. Part One: Threats, Opportunities, and Challenges
First of a two-part series The online world is now packed with applications, so it’s unsurprising that they’re a top target for threat actors. However, traditional application security (AppSec) strategies often prove ineffective. To defend themselves against the rapidly evolving threat landscape, organizations need to build a modern AppSec strategy that addresses these fast-changing conditions.
OpenAI (ChatGPT) Vulnerability Remediation Concept Work
OpenAI is an artificial intelligence research laboratory that surprised the world with ChatGPT. It was founded in San Francisco in late 2015 by Sam Altman and Elon Musk, and many others. ChatGPT grabbed 1M people's attention in the first six days, and unbelievable AI & Human conversations screenshots are still getting shared. We couldn't resist more to see how OpenAI can help developers and application security teams by sharing remediation guidance. Many application security teams manage millions of security issues on Kondukto, which would eventually save them hundreds of hours.
AppSec Decoded: Takeaways from the 2022 "Software Vulnerability Snapshot"report | Synopsys
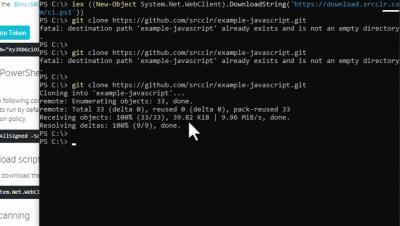
Set up an agent to scan with Veracode Software Composition Analysis
6 App Security Tips to Keep Your Application Secure
App security is essential to help deliver the best user experience possible. Read on for more information on keeping your application secure.
AppSec Decoded: Continuous AppSec testing in DevSecOps with Seeker IAST | Synopsys
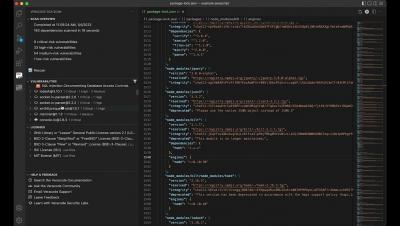
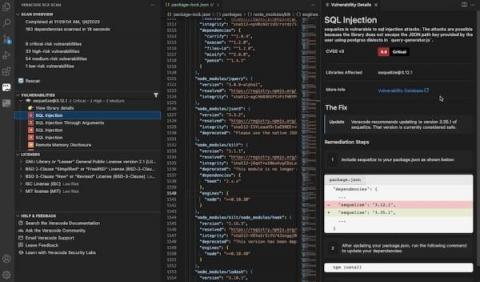
Veracode SCA Scan for VS Code Plugin
Software and AppSec Challenges and Opportunities in Banking and Fintech - Part Two
In this, the second of three blog posts, we continue to examine the issues discussed in our recent webinar, “Software and Application Security Challenges and Opportunities in Banking.” In the webinar, Rhys Arkins, Mend’s VP of Product Management, was joined by James McLeod, Director of Community of the Fintech Open Source Foundation (FINOS); Kate Stewart, VP of Dependable Embedded Systems at the Linux Foundation; and Amol Shukla, Executive Director of Engineering at Morgan Stanley, to
6 Reasons You Need to Run SCA Scans on Projects in VS Code
We love open-source software (OSS). Not only does it save time and effort, but it’s also incredibly rewarding to collaborate with other developers on major projects. Plus, it opens the door for innovation that otherwise wouldn’t be possible at this scale. However, with code comes responsibility, and so it’s imperative to understand the risk OSS libraries carry when we’re integrating them into projects.
Software and AppSec Challenges and Opportunities in Banking and Fintech - Part One
The banking and fintech industries live and die on the reliability of the online services they offer. It’s vital that the sensitive data that the industry handles is robustly protected, and that the software and applications that it uses are secure. For effective software and application security, it’s critical that banking and fintech organizations rapidly detect, identify, and remediate software vulnerabilities.
Snyk's AppSec journey in 2022
Coming off a rough and wild end to 2021 with Log4Shell in all our minds, Snyk jumped out of the gates quickly and began providing the AppSec world with new capabilities that did not disappoint. In this blog, you can review most of the key investments we made in 2022 to improve performance, add new ecosystems, and support the enterprise.
AppSec Decoded: The research behind the 2022 "Software Vulnerability Snapshot" | Synopsys
Swift and Secure Applications: Eliminating Cyber Threats
How To Do AppSec: The Application Security Guide
Modern applications are sophisticated, with different third-party software and hardware components and complicated integrations compared to legacy applications. With these complications, there is an increase in exploitable vulnerabilities in the application layer. Thus, application security is one of the most critical aspects organizations should focus on to secure their applications from cyberattacks.
How to choose React Native libraries for secure mobile application development
How to Make a Case for Buying SCA
The ongoing rise in open source vulnerabilities and software supply chain attacks poses a significant risk, and it will only increase. According to the Mend Open Source Risk Report, modern security best practices such as software composition analysis (SCA) are vital for stemming the rising tide of open source vulnerabilities in applications and software.