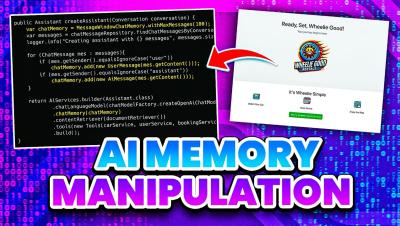
AI Chat Memory Manipulation
AI chatbots are getting smarter – but what happens when you control what they remember? In this video, I’ll show you step-by-step how AI memory can be manipulated, how that changes the way it responds, and the hidden risks this creates for both users and developers.