Easily remediate the CVEs most likely to harm you using Forward Enhanced Device Vulnerability Analysis
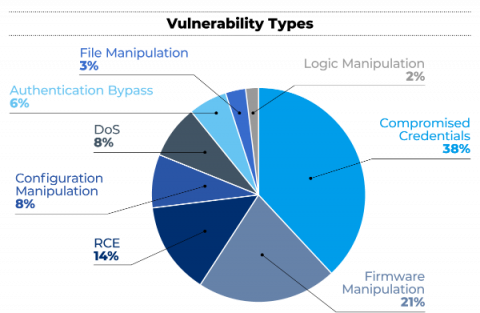
Headline grabbing vulnerabilities, like SolarWinds and Log4Shell, target management software and end hosts, but if you search for “most exploited vulnerabilities” on Google, you will quickly learn that some of them directly target network and security devices as well as server load balancers. These are the 3 most exploited CVEs in the last couple of years: Would you be surprised to learn that network device operating systems can be vulnerable to security flaws like any other software?