Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Snyk's AppSec journey in 2022
Coming off a rough and wild end to 2021 with Log4Shell in all our minds, Snyk jumped out of the gates quickly and began providing the AppSec world with new capabilities that did not disappoint. In this blog, you can review most of the key investments we made in 2022 to improve performance, add new ecosystems, and support the enterprise.
Bolstering Snyk's developer security platform in 2022
2022 was another record-breaking year for the Snyk platform. Helping an ever-growing number of customers find and fix issues across all the components making up their applications, the Snyk platform enabled over 2,500 customers during 2022 to import over 6.7 million projects, execute over 3 billion tests, and fix over 5 million issues!
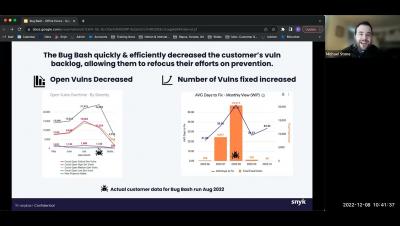
Bug Bash - How To & Best Practices - Snyk Customer Office Hours
CVE-2022-47523 - High Severity Vulnerability in ManageEngine Credential Management Products
Pen Test vs Vuln Scans - What's the difference? Cybersecurity 101
Supply chain security incident at CircleCI: Rotate your secrets
On January 4, CircleCI, an automated CI/CD pipeline setup tool, reported a security incident in their product by sharing an advisory.
Why Open Source License Management Matters
The ongoing rise in open source vulnerabilities and software supply chain attacks poses a growing threat to businesses, which heavily rely on applications for success. Between 70 and 90 percent of organizations’ code base is open source, while vulnerabilities such as Log4j have significantly exposed organizations to cyberattacks.
Watch out for DoS when using Rust's popular Hyper package
The JFrog Security Research team is constantly looking for new and previously unknown vulnerabilities and security issues in popular open-source projects to help improve their security posture and defend the wider software supply chain.
Attack Surface Management vs. Vulnerability Management: What's the Difference?
Attack surface management (ASM) and vulnerability management (VM) are often confused, but they’re not the same. The primary difference between the two is scope: Attack surface management and external attack surface management (EASM) assume that a company has many unknown assets and therefore begin with discovery. Vulnerability management, on the other hand, operates on the list of known assets.