Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Sleepless Nights Due to Malware
Automated Fuzzing | How You Can Find the Log4j Vulnerability in Less Than 10 Minutes
35 Cyber Security Vulnerability Statistics, Facts In 2023
A vulnerability is a state of being exposed to the possibility of an attack. In the context of cyber security, vulnerabilities are software bugs that can expose your systems to threats like malware infection, DDoS attacks, injections, and ransomware attacks.
What Is Vulnerability: An In-Depth Understanding
The number of devices, systems, and assets that are reliant on the internet is increasing by the day. From the POV of an attacker, this is a gold mine.
OWASP API1: 2019 - Broken Object Level Authorization
Prevent Inadvertent Software Supply Chain Exposures When Allowing Public Access to Private Registries
At JFrog, we’re serious about software supply chain security. As a CVE Numbering Authority, our JFrog Security Research team regularly discovers and discloses new malicious packages and vulnerabilities posing a threat to development organizations. We know that in order to deliver trusted software on demand, you must have a secure software supply chain — making security a priority in everything we do.
CSPRNG: Random algorithms need security too!
If I throw a coin high up in the air, I know the outcome — it will either be heads or tails. However, I can’t predict which it will be. I will certainly be able to guess with a 50% chance, but I can’t be 100% certain. If I were to roll a die, my certainty becomes less (1 in 6). However, I still know what the output could be. Computers are great at many things, especially predictability. They are deterministic and creating a truly random number is impossible.
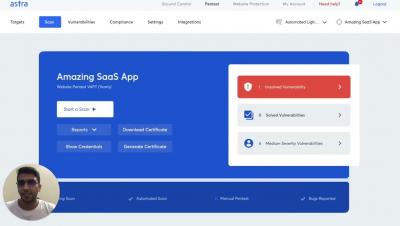
Vulnerability Management Software Comparison: Top 10 Tools
Vulnerability Management refers to the systematic approach to the identification, classification, and remediation of vulnerabilities across various cyber systems.