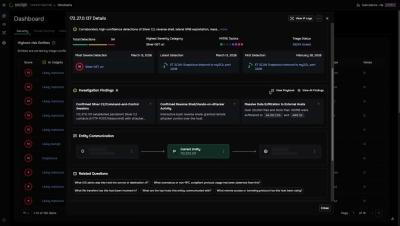
Corelight Agentic Triage overview
Corelight is excited to introduce Agentic Triage! In this demo, you can see how Agentic Triage helps SOC analysts filter through alerts and respond quickly to active threats. We combine generative AI with our industry leading log framework to identify the detections and cases that truly matter. This video shows how you can use Agentic Triage to quickly perform deep dives into open detections and make confident decisions to secure your network.