Ep 33: Too big to wing it, too small for enterprise security
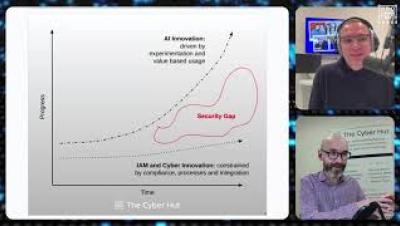
On this episode of Masters of Data, we tackle security for growing enterprises: past small business status but not quite full-scale yet. The challenge? Building effective programs with limited resources while balancing people, processes, and tools. We cover essentials like EDR, SIEM, SSO, identity management, and cloud security. The catch? Buying tools means nothing without proper implementation, tuning, and training. We explore fractional CISOs, cross-training to avoid single points of failure, and how AI supports operations.