Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Enhancing Your Operational Technology Resiliency
Maintaining cyber resilience across your ecosystem is a significant challenge that must not be brushed aside as the likelihood of experiencing a cyber incident increases year after year. For example, in 2021 alone, there were multiple attacks on Critical National Infrastructure (CNI) such as Colonial Pipeline and against the Oldsmar, Fla. water treatment plant.
3 Critical Lessons & Takeaways from the Okta Data Breach
Last month’s revelation that Okta had been hacked created a seismic impact in the world of security, with organizations still bracing themselves for the fallout from this incident. While resources, like Microsoft’s article on Lapsus$ (tracked as DEV-0537), have broadly dissected the attack vectors used in the group’s attacks, we wanted to expand on the broader trends and context surrounding the Okta hack.
Join the red team: Why every business should adopt an adversarial mindset
Netacea CTO Andy Still was recently joined on the Cybersecurity Sessions podcast by Jonathan Echavarria, an offensive security expert and Enterprise Architect at ReliaQuest. Jonathan shared his perspectives and philosophies around offensive security and what he gained from his time being part of a ‘red team’ at Facebook. Let’s recap some of the insights Andy discussed with Jonathan.
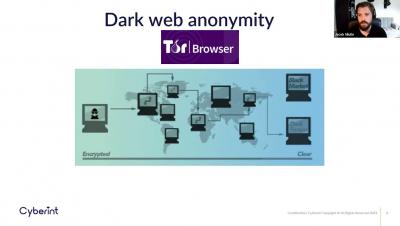
Webinar: A glimpse into the Dark Web
Spectral
State of Security Research Details Essential Strategies for the Year Ahead
This year, security teams face more challenges — old and new — and grapple with high rates of burnout. Cloud complexity, supply chain attacks and additional obstacles are pushing security teams to the limits, and inspiring new responses. New research points to key strategies that will help organizations weather the complex challenges and attacks ahead.
Why Security Strategies Should Matter to the CIO
In the face of this constant disruption, CIOs are supporting the addition, amendment, or strengthening of logistics workflows, supply chains, commercial and service delivery models, partnerships, and geographic footprints. In all of these programmes, CIOs often see cybersecurity as a hurdle—one more challenge to navigate in the path to a successful business outcome.
Automated Vulnerability Scan To Protect Your Business
A vulnerability scan is an automated process that identifies vulnerabilities (security holes) in any software, operating system, or network that bad actors can exploit. In essence, it’s an integral component of vulnerability management focused on protecting businesses from breaches and the exposure of sensitive data.
Digital Attack Surface - The Top 7 Vulnerabilities You Need to Know
In the past, the attack surface was defined and protected by the boundaries of the organization’s physical network (aka the LAN). Using physical security methods, firewalls, and careful monitoring, organizations kept their data, endpoints, and networks secure. The entire attack surface was internal, within a well-defined and fortified perimeter.