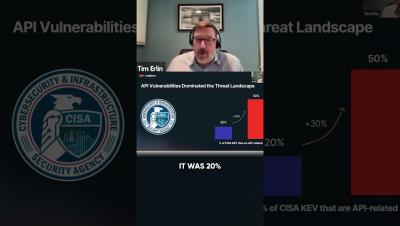
Collaborate & Protect: The Future of API Security Strategy #CyberThreats #CISAReport #APISecurity
The API attack surface is rapidly expanding, with 50% of known exploited vulnerabilities now API-related (CISA). Security leaders must prioritize API security, implement real-time monitoring, and foster cross-team collaboration to stay ahead of threats. Strengthen your defenses now!