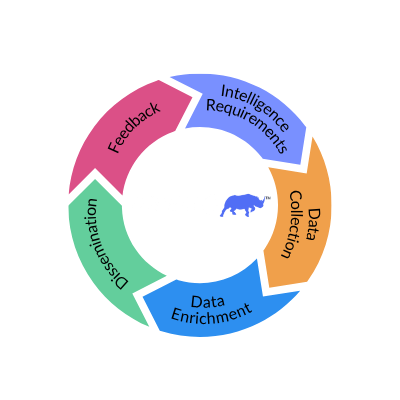
Webinar Takeaways: Automate the Threat Intelligence Lifecycle to Strengthen Defenses
Threat analysts are being bombarded with hundreds, if not thousands, of threat intel data points including new indicators of compromise (IoCs), evolving threat actor groups, shifts in regions and industries being targeted and new tools, techniques and procedures (TTPs). Security operations must be data driven so you can understand threats and efficiently allocate resources to address your most important requirements.