CVE-2025-68613: Critical RCE in n8n via expression injection
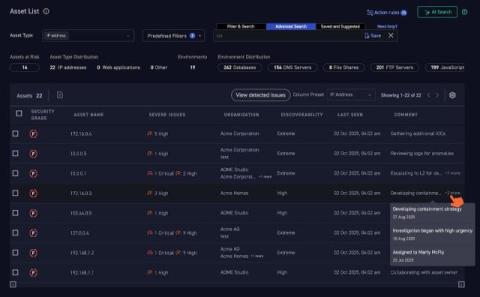
In the current AI gold rush, teams are rapidly standing up automation, AI orchestration, and integration platforms to move faster. In many cases, speed comes at the expense of visibility and security. This is where external attack surface management becomes critical. IONIX can identify and continuously monitor a wide range of AI-related and automation assets exposed to the internet, helping organizations understand what they are running, where it is exposed, and what risks it introduces.