Deep Active Browser-Based Crawling: A Must-Have in Determining External Exposure
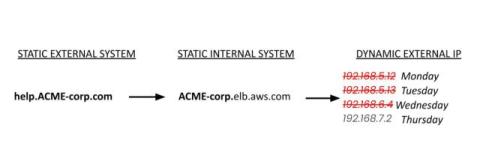
The modern internet-facing attack surface is dynamic, JavaScript-driven, and deeply interconnected with third-party services and identity providers. Accurately securing this environment requires more than passive discovery or lightweight crawling—it requires deep, active crawling that fully simulates real-world browser behavior.