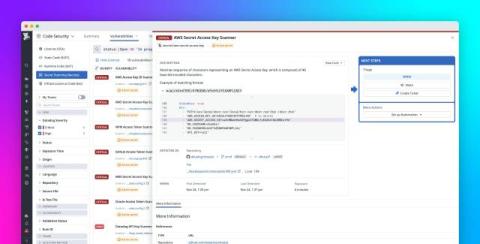
Detect and block exposed credentials with Datadog Secret Scanning
Securing secrets is a difficult task. Developers frequently hardcode credentials for quick testing or use AI-generated code snippets that include live API keys or tokens. This means that enterprise secrets can inadvertently make their way into repositories and pipelines, exposing organizations to security and compliance risks without anyone noticing. When a secret is committed to a repository, it spreads quickly across branches, becomes difficult to track, and leads to leaks that are hard to clean up.