Xona and Barrier Networks Partner to Enhance OT Access Security
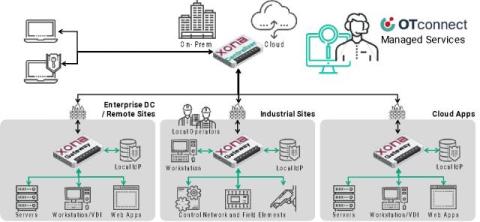
Xona Systems, a leading provider of secure access management solutions for critical infrastructure, is partnered with Barrier Networks, a managed security service provider for industrial organisations, to deliver a comprehensive, fully managed secure access solution for critical OT environments. The partnership combines Xona’s cutting-edge secure access platform with Barrier’s deep operational cyber security expertise.