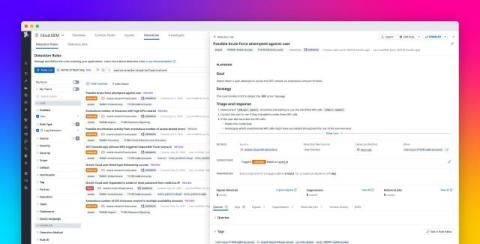
How Graylog Uses Explainable AI to Help Security Teams
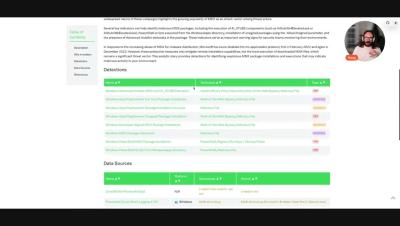
Security teams face an endless stream of alerts, false positives, and investigation backlogs. Every second counts, yet many AI-driven tools promise to handle everything for you that leaves analysts uncertain about how conclusions were made. Graylog takes a different path. The company develops assistive AI that helps analysts make faster, smarter calls with context, transparency, and control. No black boxes. No mystery logic.