Adversary Tradecraft: Exploitation of the SharePoint RCE
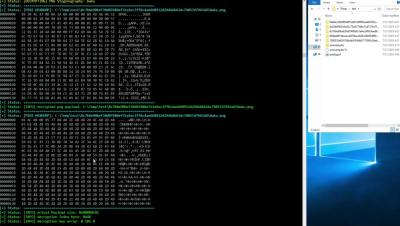
CVE-2025-53770 and CVE-2025-53771 are critical remote code execution vulnerabilities (CVSS base score 9.8) impacting Microsoft SharePoint, a widely deployed enterprise collaboration and content management platform. In this blog, we will simulate the exploitation of this SharePoint RCE vulnerability and analyze the resulting telemetry inside Graylog.