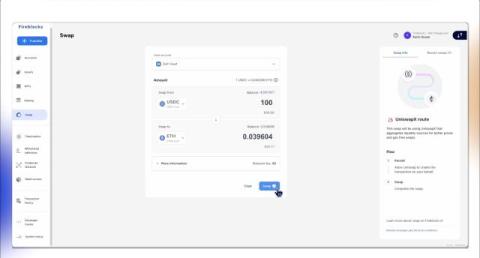
Announcing the Fireblocks MPC-BAM Protocol
The Fireblocks Cryptography Research Team has developed MPC-BAM, a new two-party ECDSA MPC protocol that achieves an ideal balance among the three key efficiency metrics in cryptographic protocols: rounds, communication, and computation. Multi-party computation (MPC) cryptography protocols are critical for the decentralized finance (DeFi) ecosystem as they enhance security and privacy while allowing direct custody operations.