Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
How to Prevent the Next Log4j Style Zero-Day Vulnerability
Software testing is notoriously hard. Search Google for CVEs caused by basic CRLF (newline character) issues and you’ll see thousands of entries. Humanity has been able to put a man on the moon, but it hasn’t yet found a proper way to handle line endings in text files. It’s those subtle corner cases that have a strong tendency of being overlooked by programmers.
Access Multiple Kubernetes Clusters
Kubernetes is a tool used by many developers and DevOps administrators to deploy and manage containerized applications, and it has become a default tool for container orchestration in many organizations.
OWASP Bay Area Meetup Host Sponsored by JFrog - April 28
Zero Trust - Replacing Depth with Logic. Identity & Access Management eSummit 2022
Is your penetration testing weak? Catch hackers at your backdoor with Sumo Logic
Demystifying Zero Trust
Zero trust is everyone’s favourite topic at the moment. But underneath its appealing phrasing lies a significant amount of market confusion over exactly what it is. Allow me to bust some myths.
Setting up Teleport (tsh) on Mac
https://goteleport.com/docs/installation/#macos
0:00 Introduction
2:00 tsh login
2:56 tsh ls
3:35 tsh ssh
3:58 tsh help
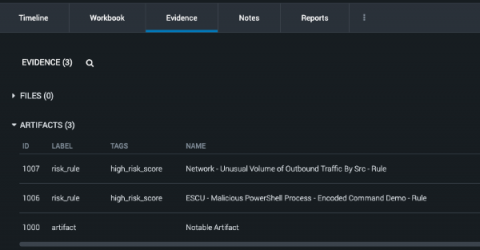
How Playbook Packs Drive Scalable Automation
No matter how advanced your Security Operations Center (SOC) is, pre-built Playbook Packs from Splunk can augment your analysts with automation that scales with your organization’s maturity. SplunkⓇ Enterprise Security (ES) users can achieve this scalable automation by using a pre-built Risk Notable Playbook Pack in Splunk SOAR.
5 Things to know about the UK's National Cyber Security Centre (NCSC)
The UK’s first cybersecurity strategy was launched in 2009 and outlined that whatever the shape of the cybersecurity mission, it made no sense to silo it away from other aspects of national security. To be effective, it had to be able to take advantage of high-grade intelligence and other security capabilities. The strategy outlined how the country needed to invest more in getting the public and private partnership really working.