Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The Dark Net's One-Stop-Shop for Cybercrime: Ransomware
Attack Surface Management (ASM): Examples, Software & the 4-Step ASM Lifecycle
An Introduction to Agile Penetration Testing
Kroll helps development teams build agile penetration testing programs that prioritize security posture throughout the project life cycle while maintaining a rapid release cadence. When it comes to modern application delivery, speed and agility are the name of the game. Customer demands are driving rapid release cycles, pushing development teams to create new products and to update existing ones at a much more aggressive pace.
ThreatQuotient Selected by Sysdig to Scale Cloud Threat Detection and Response
New Kroll report reveals notable threat trends of 2022
European Police Dismantle Cybercrime Gang Behind Euro38M CEO Fraud
Read also: GoDaddy reveals multi-year security breach, hackers targeted Asia-based data centers used by major global firms, and more.
Getting Dumped: A Trust Relationship Destroyed by Lorenz
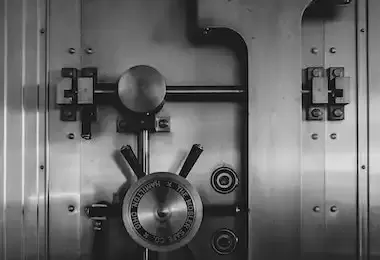
What Is GLBA?
The purpose of this guide is to provide you with a thorough understanding of GLBA as well as tips for ensuring compliance with your organization.
Stories from the SOC - The case for human response actions
As we move towards more automation, we should remember the risk of over-automating, or at least make a conscious decision to accept the risks. This is especially important in automating response actions, which left unchecked could wreak havoc with day-to-day business operations.