SAP Zero-Day CVE-2025-31324: Unauthenticated RCE in NetWeaver VCFRAMEWORK
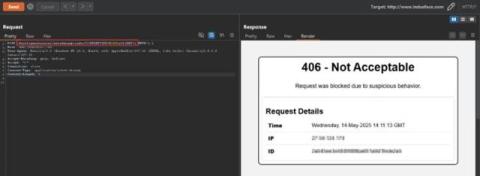
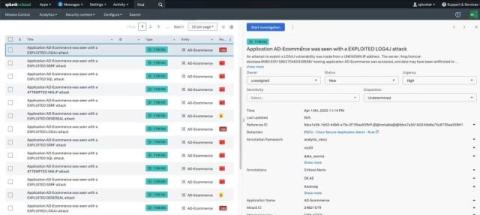
SAP disclosed a critical RCE vulnerability(CVE-2025-31324) on April 24, 2025, impacting the Visual Composer Framework in NetWeaver Application Server Java, version 7.50. This flaw poses a serious risk to enterprises relying on SAP NetWeaver for their mission-critical operations. Unauthenticated attackers can exploit this vulnerability to upload and run arbitrary files on SAP servers, potentially resulting in complete system compromise.