Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
SAST and SCA: Better together with Snyk
As applications become more complex, so does the task of securing them. While the source code making up applications consists of proprietary code, a great deal of it is also third-party, open source code. Development and security teams looking to release secure code while also maintaining a rapid pace of development, need to therefore combine static application security testing (SAST) and software composition analysis (SCA) as part of a comprehensive software security strategy.
Kubernetes Security Posture Review and Cross-Cluster Restores with New CloudCasa Release
We’re officially more than halfway through winter here in the northern hemisphere, and although that famous Pennsylvania groundhog Punxsutawney Phil has just predicted six more weeks of cold and snow, we have some good news that we think helps make up for it. We’re announcing a major new release of CloudCasa features!
Red, Purple, and Blue: The Colors of a Successful Cybersecurity Testing Program
This is the first in a series of blogs that will describe the importance of conducting Red and Purple Team exercises. The first entry in the series gives an overview of how to properly conduct these drills with follow on blogs diving deeper into the specifics of Red and Purple team maneuvers. The first realization most organizations have that their cybersecurity is, let's say, subpar generally comes right after it has been hit by a devastating attack.
Cloud Threats Memo: Why Multi-Factor Authentication is a Must-Have
Despite the growing interest in cloud accounts by opportunistic and state-sponsored actors, too many organizations fail to implement basic security measures to protect their cloud apps, such as multi-factor authentication (MFA) for administrators and users. This is the concerning finding of a report recently released by Microsoft, according to which just 22% of Azure Active Directory customers implement strong authentication mechanisms such as MFA or passwordless authentication.
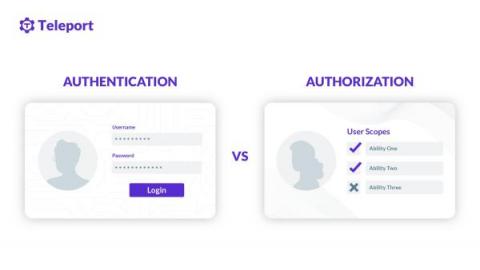
Authentication (AuthN) vs. Authorization (AuthZ)
Often referred to as AuthN (authentication) and AuthZ (authorization) in the modern access control paradigm, both authentication and authorization are a method to control access to resources. These resources can be files, programs, web applications, mobile applications, operating systems, network devices, etc. Let’s explore three common scenarios on how authentication and authorization are involved. These are the few sample cases of authentication vs. authorization.
How to Detect Data Exfiltration (Before It's Too Late)
A data exfiltration attack involves the unauthorized transfer of sensitive data, such as personal data and intellectual property, out of a target system and into a separate location. These transfers could either occur internally, through insider threats, or externally, through remote Command and Control servers. Every cyberattack with a data theft objective could be classified as a data exfiltration attack.
Application Layer Infrastructure Visibility in IaaS
The migration to cloud provides faster time to deployment and elasticity, but often at some cost and complexity to infrastructure control and visibility. A concrete example we can use is a deployment of web servers with rational security group configuration, in light of the recent Log4Shell vulnerability. While limitations are similar in all IaaS environments, consider the following AWS architecture with focus on the web servers running on EC2 instances.
What Are Azure AD Custom Security Attributes?
Microsoft released a valuable new Azure feature in December of 2021: custom security attributes. This feature is still in preview. Custom security attributes enable organizations to define new attributes to meet their needs. These attributes can be used to store information or, more notably, implement access controls with Azure attribute-based access control (ABAC). Azure ABAC, which is also in preview, enables an organization to define access rules based on the value of an object’s attribute.
Why you need Tigera's new active cloud-native application security
First-generation security solutions for cloud-native applications have been failing because they apply a legacy mindset where the focus is on vulnerability scanning instead of a holistic approach to threat detection, threat prevention, and remediation. Given that the attack surface of modern applications is much larger than in traditional apps, security teams are struggling to keep up and we’ve seen a spike in breaches.