DDoS report Q1 2024, certificate changes, QR phishing, and more
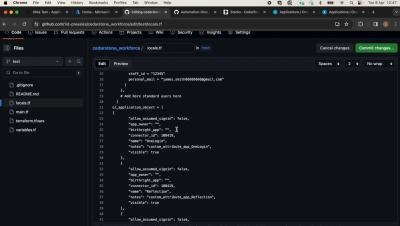
In this week's episode, we discuss different topics from blogs that we published in the previous couple of weeks, right after our Developer Week 2024. Host João Tomé is joined by our Field CTO, Trey Guinn, based in San Francisco. We discuss our most recent DDoS threat report for Q1 2024, highlighting the continued increase in DDoS attacks and emerging trends. Additionally, we address Cloudflare's efforts to ensure our customers aren't affected by Let's Encrypt's certificate chain change, emphasizing the importance of certificates.