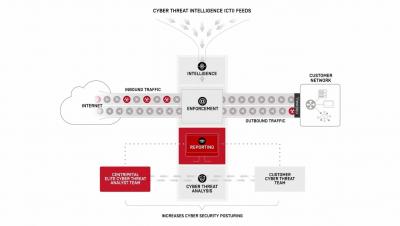
How Centripetal CleanINTERNET Works
Cyber Threat Intelligence (CTI) enables organizations to understand the current and potential threats to their business. For most, CTI’s full potential has been elusive. Until now. Zero-trust inspection and advanced shielding of all inbound and outbound traffic, powered by proactive intelligence, is the most effective strategy for network security today and is the driving force behind our industry-leading research and almost 60 patented technologies.