Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Stories from the SOC - Lateral movement using default accounts
The Windows ‘Administrator’ account is a highly privileged account that is created during a Windows installation by default. If this account is not properly secured, attackers may leverage it to conduct privilege escalation and lateral movement. When this account is used for administrative purposes, it can be difficult to distinguish between legitimate and malicious activity.
Adjusting to New Cybersecurity Regulations in 2022
How to setup Dynamic Keys in ionCube Encoder
Learn about ionCube’s most powerful feature, Dynamic Keys! In this article we will show you how to add a dynamic key based on a static value as well as the more advanced (and recommended!) non-static dynamic key! If you don’t already know about external and dynamic keys in ionCube then it would be best to start with our summary article to learn about how each feature works. We also show you how to setup a simple external key here.
Understanding Suspicious User Types With UEBA
The cybersecurity threat landscape is evolving rapidly. Hackers and other malicious users are becoming increasingly sophisticated in their attack methods, rendering traditional security tools obsolete. Modern cybercriminals will use any means to break into firewalls, send emails with infected attachments, or even bribe employees to share login credentials. Businesses in all industries must identify and implement comprehensive IT security tools and strategies to protect their valuable assets.
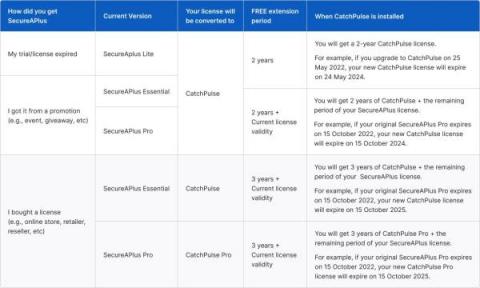
SecureAPlus users upgrade FREE to CatchPulse
SecureAge Technology recently announced the relaunch and renaming of SecureAPlus which is taking place in May 2022. The new upgraded version is now known as CatchPulse. In this post, we would like to share with our existing home customers how this change will affect your SecureAPlus Essentials and Pro installations.
Explore Corelight evidence in Humio Community Edition
Now available: A free and easy way to learn about Humio and Corelight. As part of our alliance partnership with CrowdStrike and Humio, Corelight is excited to announce a new collaboration that allows our customers and the community to experience the value of evidence.
Modernizing SAST rules maintenance to catch vulnerabilities faster
Snyk Code separates itself from the majority of static code analysis tools by generating and maintaining rule sets for its users — helping them combat common and newly discovered threats. A recent Hub article described a new Javascript vulnerability called prototype pollution, which allows attackers to modify, or “pollute”, a Javascript object prototype and execute a variety of malicious actions.
Info Stealers Ecosystem Introduction
Amazon EC2 SSH Session Recording and Auditing with Teleport
This blog is Part IV in a series about identity-based access management of AWS resources. In Part I, we covered how to use OSS Teleport to access Amazon EC2 instances running in private subnets. Part II explained implementing identity-based access via SSO integration with Okta. Part III covered the steps to configure privilege escalation for just-in-time access requests. In Part IV, we will guide you through the steps to configure SSH session recording and auditing.