How to Build an Effective Insider Risk Management Program
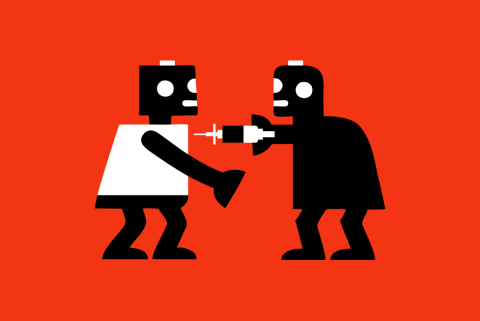
Insider threats have become one of the most difficult and damaging challenges in cybersecurity. Unlike external attackers, insiders already have access to sensitive data and systems. Their actions often appear legitimate until it’s too late. Whether it’s a malicious employee stealing intellectual property or a well-meaning one accidentally leaking customer information, insider incidents are complex, nuanced, and often invisible to traditional security tools.