Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Why EDR and NDR Tools Are Not Zero Trust Security Solutions & What to Use Instead
Lock the doors inside your home, hand out keys sparingly, then turn on an alarm in every room. Your house will get a lot more secure. However, it will also become unlivable. Tight security policies, access conditions, and subnetting configurations can take away risk but even mature Zero Trust Architecture (ZTA) environments must balance cybersecurity with usability.
DPDP Act Non-Compliance Penalties
In the dynamic realm of data protection, understanding the consequences of non-compliance is crucial. The Digital Personal Data Protection (DPDP) Act of 2023 has set forth stringent penalties for those who fail to adhere to its provisions. We’ve delved into this new act in our series of blog posts.
What does MITRE Evaluation mean for you?
MITRE ATT&CK emulates well-known threat groups inspired by publicly available threat intelligence. The evaluations do not rank vendors and their solutions; however, organizations should use them to determine which solutions best address their cybersecurity gaps, complement their existing protection implementation (network security product, existing endpoint protection solutions, etc.), and fit their business needs. The evaluation comprises two tests: Detection and prevention evaluation.
Agentless Vulnerability Management: A Complete Guide to Strengthening Your Security
This is how Maya, a devSecOps team lead at one of the prominent software development companies, started her presentation in front of Security leaders to show how the Agentless vulnerability management approach helped her: In this blog post, we’ll introduce you to Sysdig’s new Agentless scanning for vulnerability management.
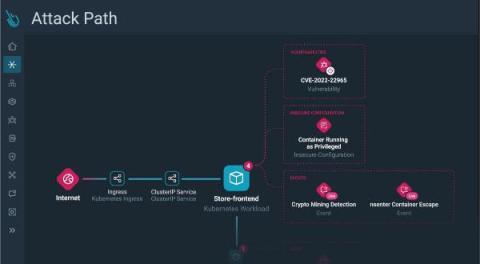
Unveiling Sysdig Secure Risks and Attack Path Analysis: Visualizing and Prioritizing Cloud Security Risks
While the cloud serves as a powerful accelerator for businesses, it also speeds up threat actors. Automation and an ever-increasing level of sophistication allow threat actors to execute complex attack chains in merely minutes, sometimes even less.The risk factors are amplified by the ability to chain together exploits and quickly move laterally in cloud environments, where a single breach could lead to a business critical compromise.
Introducing Sysdig's Enhanced Searchable Inventory for Complete Cloud Visibility
See how Sysdig’s improved inventory can help you find your way inside your ever-growing cloud infrastructure with minimal effort.
The Sysdig Cloud Attack Graph - Accelerating Cloud Native Application Protection Platform (CNAPP)
Attackers are increasing their focus on the growing cloud playing field as it becomes more lucrative. They are refining their craft to further accelerate attacks with methods like artificial intelligence and automation. Slow response times, limited coverage, and visibility gaps, often exacerbated by inadequate and fragmented tooling, allow attackers to make quick work of vulnerable environments.
When Seconds Count: Expanding Real-Time Capabilities Across CNAPP
The last few months at Sysdig have seen incredible product velocity as we accelerate our vision to create the leading cloud security platform, also known by the Gartner category Cloud-Native Application Protection Platform (CNAPP). In June, we enhanced our platform with end-to-end detection and response. Today, we are thrilled to unveil a suite of new capabilities powered by runtime insights: Skip ahead to the launch details!
Advanced SASE: It CAN Be Done Today
The Gartner® secure access service edge (SASE) framework has generated tremendous interest in the market, spanning from small businesses to large institutions, and appealing to security and networking professionals alike. Netskope is excited to announce the availability of the first secure access service edge (SASE) solution to fully address key advanced use cases demanded by large enterprises.