Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
How and Why LimaCharlie Secures Google Chrome and ChromeOS
Chrome is the world’s most popular web browser—and ChromeOS is becoming more prevalent due to the use of Chromebooks in education and other sectors. In this blog post, we’re going to talk about what this means for security teams, and how LimaCharlie can be used to secure Chrome and ChromeOS.
How to handle Node.js file uploads with Fastify
File uploading is a commonly needed functionality in web applications. Because of this, many web frameworks provide ways to allow server-side applications to accept files and work with them. This is the same with Fastify, which is a Node.js web framework that is often regarded as a successor to Express. It’s fast and highly focused on providing the best developer experience with a powerful plugin architecture and the least overhead possible.
Using Snyk reporting for data-driven security
Last month, we announced the open beta of Snyk’s new and revamped reporting. Since then, we’ve been amazed at how creative our customers have been in leveraging these new capabilities to answer all sorts of different security questions. We’re not surprised. The new reporting was designed to provide easy access to data across the Snyk platform (including Snyk Code!), and to give customers flexible analysis tools to slice and dice data as they see fit.
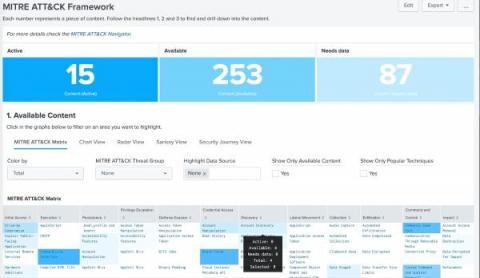
Do More with Splunk Security Essentials 3.7.0
We know the time between Thanksgiving and New Year’s is typically slow so we wanted to bring some early holiday cheer to you through the most downloaded (and free) app on Splunkbase, Splunk Security Essentials (SSE). Starting Dec. 7, Splunk Security Essentials 3.7.0 is Generally Available. We have some amazing updates in the SSE 3.7.0 release, so let’s dive right into the updates.
A Useful Cybersecurity Guide Made Specifically for Small Businesses
Modern Enterprises Require End-to-End Visibility
If you have a single vendor, single cloud homogenous network where everything is documented, you know where every device is, and you know all the possible paths in your network, then you are a networking deity. Realistically, nobody has a “simple” and fully documented network. Mainly because enterprises grew over time with the organization.
Splunk Named a Leader in the 2022 IDC MarketScape for SIEM
Splunk has been named a Leader in the IDC MarketScape: Worldwide SIEM 2022 Vendor Assessment (doc #US49029922, November 2022). We believe this recognition is a testament to our commitment to delivering a best-in-class, data-centric security analytics solution that helps our customers accelerate threat detection and investigations, and achieve cybersecurity resilience.