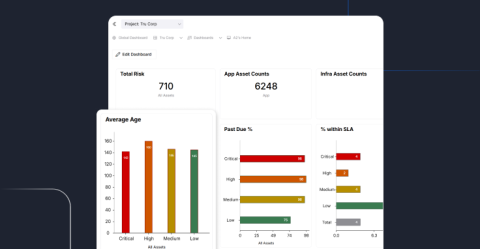
Risk-Based Vulnerability Management is the Engine Behind Modern CTEM Programs
Traditional vulnerability management once centered on scanning, enumerating, and remediating … and then repeating the process. In contrast, today’s enterprise attack surfaces shift by the hour. Cloud assets spin up and down. Business units deploy new SaaS tools overnight. Adversaries weaponize proof-of-concept exploits in days, or sometimes hours. Static, reactive processes can’t keep up.