When the Cloud Goes Dark: Why Owning Your Infrastructure Matters for Critical Services
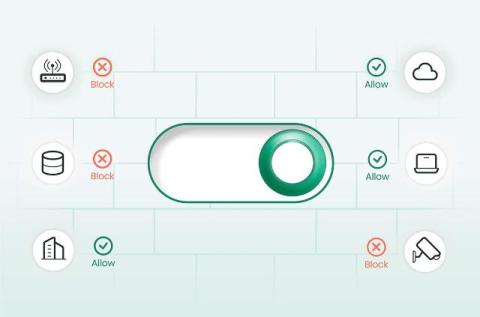
On June 12, 2025, a global outage at Google Cloud Platform (GCP) brought critical infrastructure to a halt. The ripple effects were immediate. Services from Palo Alto Networks and Cloudflare—both of which rely on GCP—experienced outages that lasted hours. Enterprises depending on these services were left blind and exposed. This wasn’t a first. It won’t be the last. But it was a wake-up call. When SASE, SSE, or SD-WAN platforms go down, the business is down. Productivity stalls.