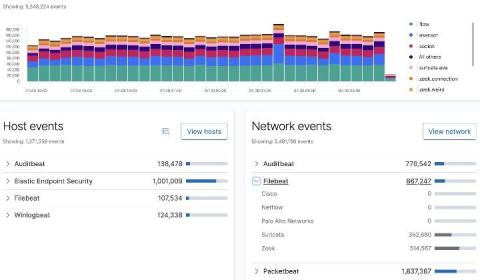
Elastic Security provides free and open protections for SUNBURST
On December 13, SolarWinds released a security advisory regarding a successful supply-chain attack on the Orion management platform. The attack affects Orion versions 2019.4 HF 5 through 2020.2.1, software products released between March and June of 2020. Likewise, on December 13, FireEye released information about a global campaign involving SolarWinds supply-chain compromise that affected some versions of Orion software.