How Internal Scanning works: Q&A with Detectify's product expert
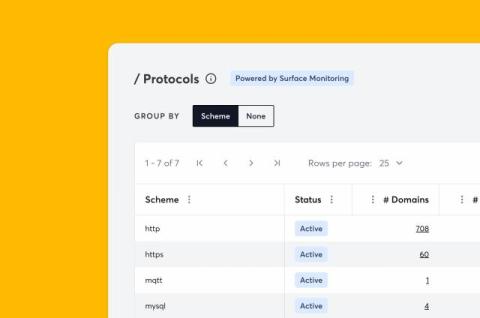
Security doesn’t stop at the perimeter. The “inside” of your network often harbors many overlooked risks. To address this, ealier this year we launched Detectify Internal Scanning, designed to bring our world-class vulnerability research directly into your private ecosystems.