Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
How to Secure Your Container Registries With GitGuardian's Honeytoken
Discover how to enhance the security of your container registries using honeytokens. Learn the steps to secure Docker Registry, GitHub Container Registry, and GitLab Container Registry with honeytokens. Strengthen your DevOps pipeline and protect your valuable assets.
What is CISPA? A Guide to the Cyber Intelligence Sharing and Protection Act
DFARS Compliance: What You Need to Know
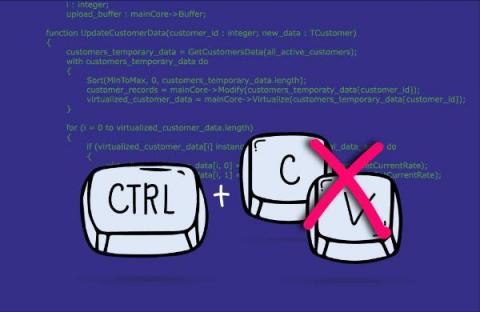
Why You Should Avoid Copy and Paste Code
So many things seem like a good idea at the time. The Red Sox selling Babe Ruth to the Yankees. Decca Records rejecting The Beatles. “New” Coca-Cola. Blockbuster passing on buying Netflix. The formation of Nickelback. Just popping into Ikea for a “quick” look around. Of course, we know differently. And the same can be said about copying and pasting code.
Understanding the Zero Trust Security Model
Are you looking for ways to transform your organization’s network security for the modern era? Zero. Zero. Trust security offers a cutting-edge approach that eliminates implicit trust and requires continuous verification of users and devices. Dive into this comprehensive guide and discover how Zero Trust can revolutionize your security posture and protect your valuable resources.
Is it time for a "cyber defense" strength and conditioning program?
They say the best way to stay healthy and maintain fitness as we age is through strength, conditioning, nutrition, and exercise. In the same way, as organizational cybersecurity efforts weaken with age they need to be analyzed and strengthened. Is it time to regain your organization’s cyber security in the weight room? Is it time for a cybersecurity personal trainer of sorts?
ATM Transaction Reversal Fraud: Strategies to Safeguard Your Finances
Picture a quaint, small town enveloped in the tranquility of a peaceful night. The only signs of life are flickering street lamps and the glow from the neighborhood automated teller machine (ATM). You spot someone approach the ATM, withdraw cash and walk away. It all looks so normal. What you don’t realize is that you have just witnessed a fraud attack, specifically, transaction reversal fraud (TRF).
Guide to User Access Review: What Is It, Best Practices, and Checklist
Every company has workers that have been there from the beginning and worked in every department. Knowledge of the company’s processes makes them valuable employees, but they can also access and put at risk lots of sensitive data. Regular user access reviews can help you mitigate this risk and safeguard your critical assets. Regularly reviewing user access is an essential part of access management.