Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Why Companies Choose MSSPs for Unified Security
Cyber threat intelligence is gaining popularity in today's digital landscape, as organizations face many security threats that can compromise their sensitive data and disrupt their operations. To effectively reduce these risks and further advance threat detection, many companies are turning to Managed Security Service Providers (MSSPs) for unified security solutions. In this blog post, we will explain why companies choose MSSPs and the advantages of MSSPs for unified security.
The Ins and Outs of Application Security Policy
A policy, by definition, is a statement of management intent that is mandatory for an organization. A security policy, obviously, focuses on the security of information assets.
Trustwave 2024 Cybersecurity Predictions: Artificial Intelligence and the US Presidential Election
There is every reason to believe that 2024 may be an interesting year in the cybersecurity space, making it difficult to foresee what might transpire. However, Trustwave's leadership is up to the task. There are several issues that Trustwave already knows will be at the core of many challenges that the world will have to face next year.
The best Cybersecurity conference you never heard of
For the past 12 years in Austin, TX, the last week of October has been reserved for the Lonestar Application Security Conference (LASCON). Unequivocally, LASCON is the best cybersecurity conference you have never heard of! LASCON is the annual confab of the Austin, TX OWASP (the Open Worldwide Application Security Project) chapter. OWASP is a volunteer organization that is a treasure trove of application security information with things such as standards, discussion groups, documentation, and more.
Holiday Scams Include Thousands of Impersonation Phishing Domains per Brand
Midstride in this year’s holiday shopping, it’s important to realize just how many websites exist that impersonate legitimate online retailers. More importantly, your users need to know how to spot these types of attacks before falling victim.
New Remote "Job" Scam Tells Victims They'll Get Paid For Liking YouTube Videos
Researchers at Bitdefender warn that scammers are tricking victims with fake remote job opportunities. In this case, the scammers tell victims that they’ll get paid for liking YouTube videos. Notably, the scammers send the victims a small amount of money (around six dollars) to gain their trust. After this, the victim is invited to a Telegram channel, where the scammer offers to give them much higher-paying tasks if they pay an entry fee of between $21 and $1,083.
The Current Challenges of Adopting Zero Trust and What You Can Do About Them
In the fast-evolving world of cybersecurity, the transition to remote work, the challenges of Zero Trust adoption, and the technology that supports it have taken center stage. Join me as we explore the insights of cybersecurity professionals and uncover the realities of this transformative journey.
The History of Patch Tuesday: Looking back at the first 20 years
One of the most critical aspects of cybersecurity is ensuring that all software is kept up to date with the latest patches. This is necessary to cover any vulnerabilities that cybercriminals could take advantage of in order to infiltrate an organization and launch an attack. With the volume of updates and the effort needed to install and configure them, it is good to know precisely when patches will be released.
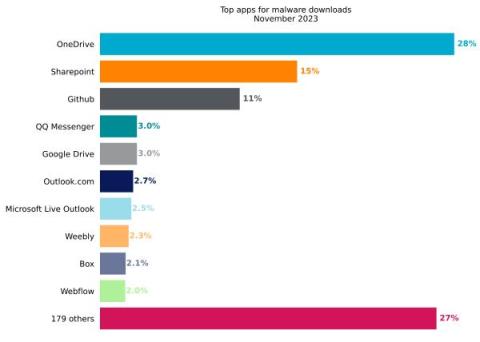
Netskope Threat Labs Stats for November 2023
Netskope Threat Labs publishes a monthly summary blog post of the top threats we are tracking on the Netskope platform. The purpose of this post is to provide strategic, actionable intelligence on active threats against enterprise users worldwide.