Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Docker Vs. Kubernetes: A Detailed Comparison
The Docker vs. Kubernetes debate is common in the containerization world. Although most people like comparing Kubernetes and Docker, the two technologies are not exchangeable—you cannot choose one over the other. They are essentially discrete technologies that can perfectly complement each other when creating, delivering, and scaling containerized applications. In fact, the best at par comparison would be Docker Swarm vs. Kubernetes, which we’ll talk about later.
Python now fully supported in Snyk Code
Earlier this year, we announced the beta support for Python in Snyk Code. This beta period gave us the chance to let customers have access to our extensive collection of Python rules while we finished our knowledge base review and added curated content. We are happy to announce that this work has concluded, and Python is now a fully supported language. 🐍 🎉
Mitigating and remediating intent-based Android security vulnerabilities
In previous posts we explored the potential for intent-based Android security vulnerabilities and then used Snyk Code to find exploits in popular apps on the Google Play store. If you know Snyk, you also know there’s no way we can just point out vulnerabilities and not recommend fixes. Analyzing such an extensive dataset enabled us to review a lot of code.
Going Beyond Exclude Patterns: Safe Repositories With Priority Resolution
You probably remember the Namespace Shadowing a.k.a. “Dependency Confusion” attack that was in the news a couple of weeks ago. I blogged back then about the Exclude Patterns feature of JFrog Artifactory which we’ve had forever and was always intended to protect you against those kinds of attacks.
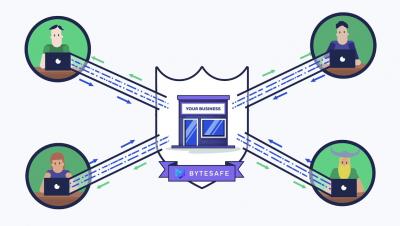
Introduction to Bytesafe in 1 min
Snyk debuts on 2021 CNBC Disruptor 50 List at #15
We are honored to share that Snyk has been named to the ninth annual CNBC Disruptor 50 List, coming in at #15! The full list, unveiled earlier this week, identifies 50 private companies “aligned with today’s rapid pace of technological change and poised to emerge from the pandemic as the next generation of business leaders.” The pandemic accelerated digital transformation and associated cybersecurity concerns.
Top Tips for Technical Due Diligence Process
We all dream of creating the next big thing: getting that investment that will help us over the finish line, landing a partnership with one of the big players, or getting acquired by a global enterprise. But as we race to keep ahead of the market and surprise our customers with bigger and better offerings than they ever imagined, we have to pass that dreaded series of hurdles: technical due diligence.
Hunting intent-based Android security vulnerabilities with Snyk Code
In our previous blog, we explored the nature of intent-based Android security vulnerabilities. Now we’re going to dive into how we performed our security analysis on apps in the Google Play Store with Snyk Code.