Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The latest News and Information on Data Security including privacy, protection, and encryption.
Maximizing Efficiency: The Significance of TDM for Sensitive Data
Looking to 2024: Data, AI and security will be top priorities for businesses
7 Effective Security Measures to Combat Cyberterrorism
New at Nightfall: November '23 Product Updates
This month has been full of new feature announcements, as well as various improvements to security team workflows. Read on to learn more about how you can leverage Nightfall's latest offerings.
CISO Advisory Board Response to The State of Data Security: Securing an Uncertain Future
Rubrik Zero Labs’ recent study accentuated several hard truths we think are important and warrant a response from Rubrik’s CISO Advisory Board. First, let’s confirm what many of us have already discussed: It’s not fun to be a CISO right now. There’s an overwhelming amount of expectation—from the board to business unit owners—to figure out how to grow and use data, but also keep it secure, and figure out what happens when it’s not.
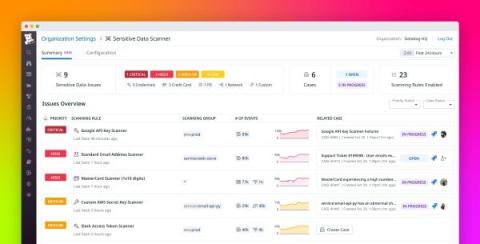
Discover, triage, and remediate sensitive data issues at scale with Sensitive Data Scanner
Managing sensitive information in your telemetry data poses many challenges to governance, risk management, and compliance (GRC) teams and overall security. Organizations in healthcare, finance, insurance, and other fields must carefully adhere to strict compliance requirements. But sensitive data comes in many forms and moves between many endpoints, and as a result, it can easily become exposed in telemetry data.