Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Cloud security fundamentals part 3: Empower your developers
In our previous blog breaking down The 5 Fundamentals of Cloud Security, we looked at the value of prevention and secure design. Mapping resource relationships and enforcing security guardrails throughout development helps greatly reduce an available attack surface. But who will enforce these guardrails when your security team is busy with other work? This should be where developers are able to step in. So let’s look at another vital element in cloud security: empowering developers.
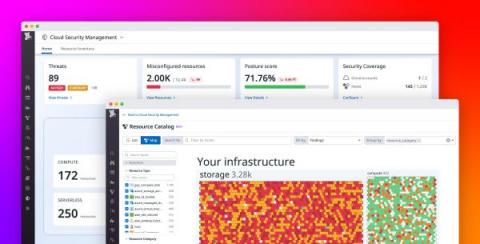
Add security context to observability data with Datadog Cloud Security Management
Organizations are rapidly migrating their infrastructure to the cloud, enabling them to modernize their applications and deliver more value to their customers. But this transition creates significant security risks that they may be unable to keep pace with. For example, cyber attacks on cloud resources are becoming more sophisticated and prevalent. Additionally, organizations often rely on legacy, disjointed security tools that don’t integrate well with cloud-native infrastructure.
Micro Lesson: Security Automation with Cloud SOAR Playbooks
CloudCasa Helps Overcome Day 2 Kubernetes Challenges and Integrates with the 3 Major Cloud Providers
In this episode of TFiR Let’s Talk, Swapnil Bhartiya sits down with Sathya Sankaran, COO of Catalogic and GM of CloudCasa, to discuss in-depth how CloudCasa is supporting backup for the three major cloud providers − Azure Kubernetes Service (AKS), Amazon Elastic Kubernetes Service (EKS), and Google Kubernetes Engine (GKE) − and the data protection challenges they are addressing.
10 Tips to Mitigate Your SaaS Cybersecurity Risks
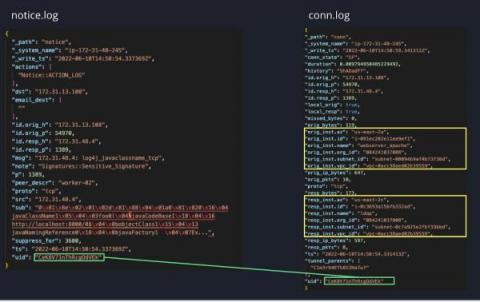
"Easy" button for cloud NDR visibility
As organizations continue to rapidly adopt cloud services, they struggle to expand network detection and response (NDR) capabilities to their hybrid and multi-cloud environments. Network visibility is critical for security operations center (SOC) teams to secure their cloud environments and ensure they can elevate threat detection and incident investigation capabilities. However, traditional NDR solutions require management, configuration and often lack the security context needed.
Automate Keeper Device Approval in the Cloud with Azure
Keeper’s powerful Automator eliminates the repetitive task of device approval for Keeper administrators. With Keeper Automator, users will enjoy instant access to Keeper on any new device without having to wait for manual administrative approval. Now with Microsoft Azure support, administrators can deploy Keeper Automator to an Azure Container Service, providing a fully cloud hosted instance of Automator.
Falco Plugins - Introduction to Falco Plugins
Do You Know Who's in Your Cloud? Preventing Identity-Based Threats with CIEM
As organizations continue to shift to multi-cloud environments and increasingly use cloud services for application development, new challenges emerge that require dramatic changes in the delivery and practice of cybersecurity.