Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Defending Against Cloud Security Threats: Breaking Down Initial Access Techniques
As organizations continue to move their business operations into the cloud, the expanded attack surface generated by the “digital transformation” continues to present new opportunities for threat actors. Luckily, strategies to mitigate these new risks do exist and, as always, these center around the techniques and tactics of the adversaries.
How to deal with ransomware on Azure
Let’s dig deeper into the techniques used by attackers and the mitigations you should implement when ransomware on Azure affects you. By now, we should all be aware of ransomware from the constant news articles associated with this known threat. As we explained in the anatomy of a cloud attacks, ransomware is a way for attackers to make money when they gain control of your accounts through data encryption, therefore restricting your access to the system.
Exchange: Devo 360 for AWS application
What Is Cloud Detection and Response and Why Do You Need It?
How Do Hidden Web Trackers Put My Privacy at Risk?
Cloud security fundamentals part 4: Align and automate with policy as code
Security policies are still awaiting digital transformation. A key phrase in today’s cloud-driven world, “digital transformation” generally refers to the ongoing work of digitizing formerly paper-based processes. “Paper,” however, is not literal — many processes don’t use paper, but still flow as if they were. Uploading a document to Google Drive, in other words, doesn’t amount to digital transformation.
Top 5 Tips on Avoiding Cloud Misconfigurations
Cloud misconfigurations can cause devastating financial and reputational damage to organizations. Yet, such undesirable circumstances can be avoided by understanding the common misconfiguration errors and mitigating them before malicious actors can exploit them. Ava Chawla, AlgoSec’s Global Head of Security provides some valuable insights on cloud misconfigurations and offers useful tips on how to avoid them.
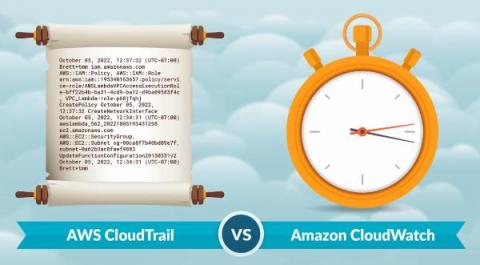
Does cloud log management shield you from threats? CloudTrail vs CloudWatch
What is different about cloud log management versus on-premises? The answer may seem simple, but several elements such as CloudTrail vs. CloudWatch come into play. In this article, we will cover some of the most important differences, and then dig deeper into a specific example of AWS CloudTrail vs. CloudWatch.
How Government Agencies Can Secure Mission Critical Software in the Cloud
Government agencies are instructed by Executive Order to improve the delivery of digital services to citizens while also safeguarding critical data and systems. Often, this leads to a difficult decision between speed of application production and software security. However, as recent events have shown, sacrificing security in the name of speed compromises the safety of citizens and government infrastructure.