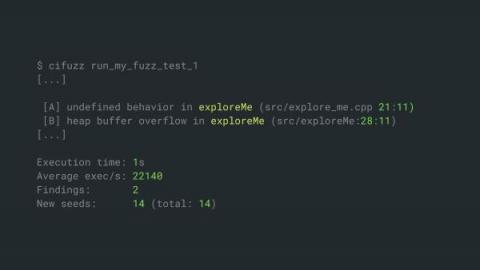
SAST - All About Static Application Security Testing
Static Application Security Testing (SAST) has been a central part of application security efforts for more than 15 years. Forrester’s State Of Application Security Report, 2022 found that lacking application security remains a leading cause of external security breaches, so it’s safe to say that SAST will be in use for the foreseeable future.