Why You Can't Secure APIs You Don't Know Exist #APIsecurity #ShadowAPIs #Cybersecurity
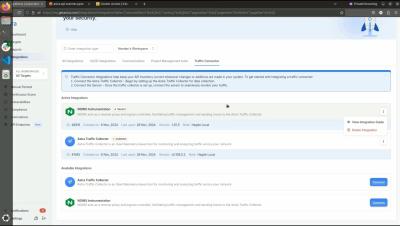
Most orgs don’t even know how many APIs they have. And if you can’t see them — you definitely can’t secure them. Wallarm shows why API visibility is the foundation of modern protection.