Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
%term
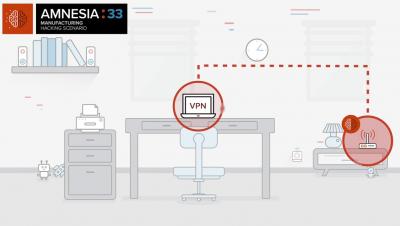
How to identify and mitigate risk from AMNESIA:33 vulnerabilities
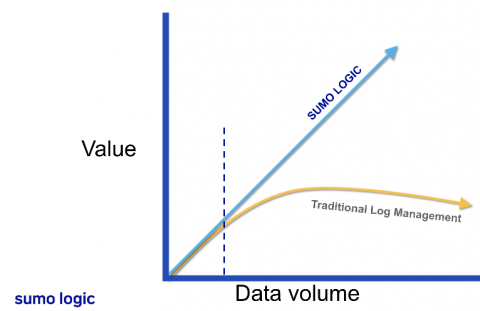
Building your modern cloud SIEM
See Netskope Prove It
Tighten Up Your Strategy: Evaluating the Leakiness of a Cloud App
We at Netskope Threat Labs have published a series of blogs detailing the misconfigurations in cloud apps causing data exposure. Misconfiguration and sensitive data exposure have been listed as predominant top 10 OWASP security risks for years, and are now also the predominant cause of cloud data breaches.
What is Access Control?
Access control is a security technique that regulates who or what can view, use or access a place or other resources. It is a fundamental concept in physical security and information security designed to minimize risk. At a high level, access control is about restricting access to a resource. Any access control system, whether physical or logical, has five main components: Access control can be split into two groups designed to improve physical security or cybersecurity:
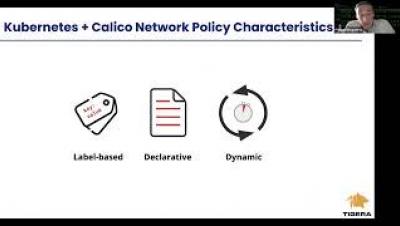
Securing Kubernetes using Egress Access Controls
Government and Education Have the Highest Percentage of Apps With Security Flaws
It’s been a stressful year, to say the least, for the government and education sector. Government organizations were challenged with pivoting their operations to a digital model while schools were forced to decide between hybrid or remote learning programs for their students. The rise of digital operations has made application security (AppSec) more important than ever.
The Year of the Pandemic and 2021 Cybersecurity Predictions
2020 will always be remembered as the year our lives changed dramatically due to the Coivd-19 pandemic. Here our panel of security experts look back at the lessons learned in the past 12 months and share their predictions for the key security challenges organizations will face in 2021.
How to Choose a Credible Cloud Security Software Vendor
There is no shortage of IT cloud software services out there for businesses to choose from. Regardless of their business needs you can be sure there will be a myriad of solutions. Instead of a few grand does-it-all services, IT has become a swarm of inter-playing, inter-operating, and interconnecting services. It’s no surprise that services like zapier and IFTTT are thriving in this ecosystem where they can become the glue and automate the gap between them. The future is surely bright.