Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
%term
Cryptocurrency exchange Binance offers $290,000 bounty to unmask blackmailer
Binance, one of the world’s largest cryptocurrency exchanges, has revealed that it is being blackmailed to the tune of 300 Bitcoin (approximately US $3.5 million) by someone who is threatening to release some 10,000 sensitive photographs of its customers. And in an attempt to identify its blackmailer, Binance has put a 25 Bitcoin (approximately US $290,000) bounty on their head.
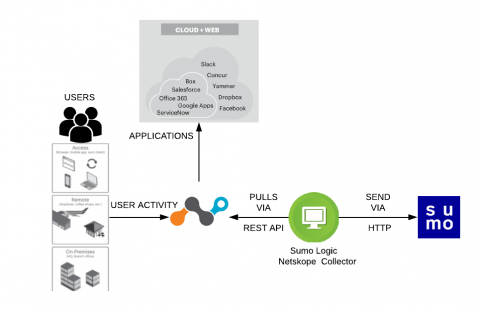
Sumo Logic adds Netskope to its Security and Compliance Arsenal
Living the 7 Habits of Highly Effective Cybersecurity
The recent Tripwire blog ‘7 Habits of highly effective Vulnerability Management’ by Tim Erlin was a great read with some sage advice on the always relevant security topic of VM. I noticed, however, that although the seven points themselves were all Tim’s own, the title snappily paraphrased Steven Covey’s classic management book. This made me think.
Best Practices for IT Security Teams in the Age of Cloud
About a decade ago, organizations were hesitant to adopt cloud solutions, with many citing security concerns. Fast forward to 2019, and 81% of organizations have a multi-cloud strategy, spurred on by the desire for increased flexibility, usage-based spending and desire to respond to market opportunity with greater agility.
Tigera Secure 2.5 - Implement Kubernetes Network Security Using Your Firewall Manager
We are excited to announce the general availability of Tigera Secure 2.5. With this release, security teams can now create and enforce security controls for Kubernetes using their existing firewall manager.
What Is the Difference Between SIEM and SOAR?
Nowadays, a lot of attention is being paid on the SOAR vs. SIEM debate. To get the most benefit from your security data, it is vital to understand the difference between these essential cybersecurity tools. Although SOAR and SIEM have several components in common, we cannot use these tools interchangeably as they are different in nature.
How to browse the internet anonymously
Browsing privately ensures that no one spies on what you do online. Thanks to the tech growth that the world has experienced over the years, you either choose to browse the entire web anonymously or if you only need to hide from specific spies, you can opt to make all of your visits to a single website anonymous.
Introducing Asset Inventory: stay on top of your web asset security
Good security starts with knowing your web assets. To enable transparency over your tech stack, we have released Asset Inventory, a new view that helps you prioritize security issues and collaborate across teams to stay on top of your web asset security. This release is the first step towards broader asset tracking functionality in Detectify.
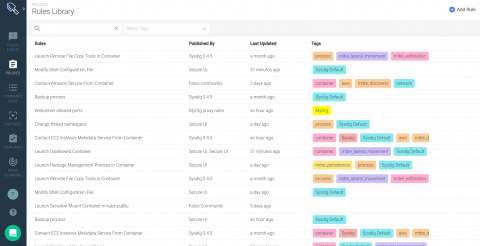
Introducing the new Sysdig Secure policy editor
Among many other features Sysdig Secure version 2.4 introduces a new and improved runtime policy editor, along with a comprehensive library combining out-of-the-box run-time policies from our threat research teams, container-specific compliance standards, Kubernetes security and Falco opensource community rules.